Confused by terms like PKCE, HttpOnly, or OIDC? Here’s a friendly, no-fluff glossary of the most common security terms every developer, architect, and product person should know.
Concepts
Learn how the Backend for Frontend (BFF) architecture helps secure OAuth and OIDC flows in modern apps by safely handling tokens, reducing attack surfaces, and enabling cleaner session management.
Confused why SSO works in Edge but not Chrome? Wondering if Okta can deliver seamless login across macOS and Linux? This deep dive into SSO explains how browsers, identity providers, and platforms affect your authentication experience — and what to do about it.
OAuth 2.0 and OpenID Connect (OIDC) are powerful, flexible, and… surprisingly easy to misconfigure.Note: This article belongs to Part 5.2: App Security Best Practices in our Application Security series. From overly permissive tokens to incorrect redirect URIs and unchecked ID tokens — even mature teams fall into subtle traps. In this final post of […]
Why the Implicit Flow is deprecated and how PKCE (Proof Key for Code Exchange) secures modern Single Page Applications (SPAs) and mobile apps using OAuth 2.0.
Dive into the structure of JSON Web Tokens (JWT), how they're signed and validated, where expiry pitfalls creep in, and best practices for secure token usage in real-world applications.
By now, you know the difference between authentication and authorization. You’ve explored OAuth 2.0, OpenID Connect, and even federated SSO setups across identity providers. So, what’s next? Have you ever heard or Refresh Tokens?Note: This article belongs to Part 4.1: Token Lifecycle & Retry Logic in our Application Security series. Here’s the […]
Federated Identity enables Single Sign-On across different systems, domains, and organizations. Learn how it works, what protocols are involved, and how trust is brokered between Identity Providers and applications.
Active Directory and Azure AD both manage identities in Microsoft environments—but they serve very different purposes. This blog breaks down how they work, where they differ, and when to use each in modern application architecture.
LDAP is still widely used for centralized authentication and user directories in enterprise systems. This post breaks down how it works, how it compares to modern identity solutions, and how to integrate it as a developer.
SAML powers enterprise SSO for millions of users every day. Learn what it is, how it works, and how to implement it with Spring Security in modern applications.
OpenID Connect adds identity on top of OAuth 2.0. Learn how it works, when to use it, and how to implement secure login flows using Spring Security.
OAuth 2.0 is the backbone of modern authorization. Learn how it works, which flows to use, and how to implement OAuth securely using Spring Security.
Explore the core differences between session-based and token-based authentication. Understand the technical design, implementation trade-offs, and how Spring Security supports both approaches.
Authentication identifies who a user is. Authorization defines what they’re allowed to do. Learn the technical distinctions with Spring Security examples to apply these concepts in your applications.
Kick off your journey into Application Security with this visual overview of modern authentication, authorization, and identity protocols. From OAuth to LDAP, this series maps out everything you need to build secure, user-aware applications.
Containerization packages software for easy deployment across any system. These lightweight units, faster than VMs, enable efficient microservices and cloud-based applications.
Learn how to use arrays in Java with this comprehensive guide. Includes information on declaring, accessing, and iterating through arrays, as well as examples of 2D and 3D arrays.
Learn all about proxy design pattern with examples. How and when to use and implement them. Also, learn the benefits and drawbacks of using proxy design patterns.
Discover how Data Structures & Algorithms (DSA) go beyond interview prep to reshape your problem-solving mindset. Real-world examples of stacks, queues, graphs, heaps, and more.
Arrays, Linked lists, Stacks, Queues, Trees, and Graphs are a crucial part of Data Structure. Searching & sorting algorithms are used to get the most out of it.
Object-oriented programming, commonly known as OOPs is a programming style to solve a problem using encapsulation, abstraction, inheritance, and polymorphism.
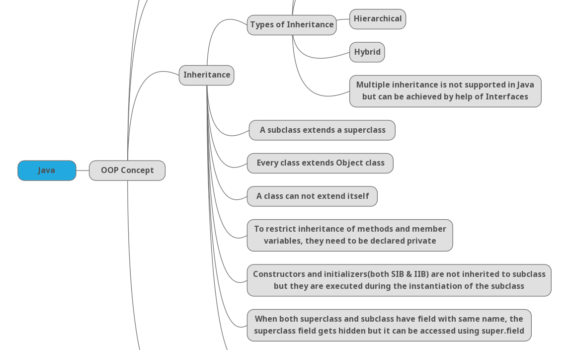
Inheritance in Java is one of the four pillars of OOPS. It depicts a parent-child relationship between classes. It follows an order of execution of constructors.
Commonly referred to as OSS (Open-Source Software) or FOSS, it permits you to use the source code or any such artifact which comes under the open-source license